
Table Of Contents
- What Is Backdoor?
- How Do I Clean My Hacked Website From Backdoors?
- 1. Keyword Identification
- 2. JavaScript Injections
- 3. Comparing WordPress Core Files For Differences
- 4. Comparing Plugin Files For Differences
- 5. Search PHP Files In The Uploads Folder
- 6. Check The .htaccess File
- 7. Search For Modified Files
- 8. Unknown Files And Folders
- 9. Other Backdoor Detection Methods
- What Are WordPress Security Plugins?
- Malcare – Best WordPress Hacking Solution
- How To Use MalCare To Remove Backdoors?
- Share this post
Is Your WordPress Website Getting Hacked Repeatedly? Here’s How to Stop It!
Are you looking for the best WordPress hacking solution? You have reached the right place!
Website getting hacked over and over again? It must be a nightmare!
You must be wondering how hackers are getting access to your website. There must be a loophole that is being exploited.
That loophole is a ‘backdoor’.
Yes! Your business website has a backdoor using which hackers are sneaking into your site.
Backdoors are usually hidden and hard to find!
However, a powerful scanner can detect hidden backdoors that can then be removed using a malware cleaner.
In this article, I’ll show you how to get rid of backdoors but first, let’s learn about backdoors.
What Is Backdoor?
Imagine your home getting burgled over and over again as the burglar has found a way to enter through your backdoor.
For example, he has a duplicate backdoor key that he can use whenever you are not at home.
So, until you change the lock or use some other means, he can keep coming back and intrude on your property.
The backdoor in your WordPress website is somewhat similar to your house backdoor. Hackers can keep using this backdoor to access and damage your WordPress website.
So, why are backdoors so challenging to detect as compared to normal malware code?
This is because backdoors look like any other WordPress file and are stored in WordPress folders that you mostly won’t bother to check.
For example, in Core WordPress folders (for example, the “wp-includes” folder) or as a new WordPress plugin/theme.
How Do I Clean My Hacked Website From Backdoors?
Though detecting and cleaning hidden backdoors may seem challenging, it is certainly possible!
Most WordPress website owners use the following manual methods to scan and remove backdoors from their websites.
However, we would advise you to try the below methods only if you have the required WordPress technical knowledge.
Now, let’s evaluate each method of backdoor detection.
1. Keyword Identification
A standard method of detecting backdoors is to search for keywords such as “eval,” “shell-exec,” “base64_decode,” or “gzuncompress” that are usually found in malicious malware code.
To execute this operation, you should be familiar with Linux commands like Find, Grep, and Stat.
A limitation of this method is that while such keywords are used in backdoor code, they are also used in “legitimate” WordPress files and plugin code.
Hence, this method can end in a higher number of false positives or even hamper your WordPress website functionality as you may end up removing useful code.
2. JavaScript Injections
This method is commonly used if your website is constantly redirecting from your home page to some other site. There are two ways to fix this issue:
- Visit and look up the page source of your website’s home page. To identify the code script that is causing the redirection, execute the “Grep” command, and then remove the script.
- If your website is redirecting without first landing on your home page, execute the “Wget” command that generally prevents the execution of all JavaScript code.
3. Comparing WordPress Core Files For Differences
This backdoor detection method is used to compare the Core WordPress files (in your installed website) with the core files from the official WordPress repository and to identify differences if any.
This method is quite useful as long as the same WordPress version of the core files is being compared.
However, a major limitation of this method is that backdoors do not necessarily have to infect the core files only in any WordPress installation. They can most likely also infiltrate other files and folders.
4. Comparing Plugin Files For Differences
Similar to comparing WordPress core files, this method is used to compare any differences between the plugin files (installed on the WordPress website) and same plugins downloaded from the official WordPress plugin repository.
Although very time-consuming, this method is fairly effective when comparing plugins with the same version.
However, this method is also unreliable as all WordPress plugins that are downloaded are not publicly available. Some of them may not even be listed in the WordPress repository.
5. Search PHP Files In The Uploads Folder
Hackers often store PHP files (with backdoors) in the Uploads folder of your WordPress installation.
To detect PHP files in this folder, you can run this command:
Find uploads –name “*.php” -print followed by deleting the PHP files from the folder.
However, you could accidentally delete legitimate PHP files that are usually a part of valid plugin installation. This could lead to your website breaking.
6. Check The .htaccess File
If hackers gain control of your website’s .htaccess file, they can make many modifications to damage your website.
For example, to implement website redirects or to execute the .htaccess file as a .php file. Check for any recent modifications in this file to detect backdoors.
7. Search For Modified Files
This method comprises searching for backdoors in newly uploaded or recently modified WordPress website files.
This method is usually effective in narrowing down the website files that you need to search for backdoors.
However, it is ineffective if the hacker is smart and resets the date and time stamp of the modified files.
8. Unknown Files And Folders
Most WordPress website owners do not access the root folder of their WordPress installation, namely the public_html folder making this the target folder for hackers to store backdoors.
Other vulnerable folders include the plugins folder (/wp-content/plugins) and the themes folder (/wp-content/themes) located within the public_html folder.
This method involves searching for backdoors in new or unknown files and folders within these highly vulnerable folders.
However, you could end up accidentally deleting new files and folders that are part of a safe WordPress plugin/theme installation.
9. Other Backdoor Detection Methods
This includes checking for any rogue plugins/themes or unauthorized user accounts.
Each of these manual backdoor detection methods requires plenty of technical knowledge and cannot be executed by a novice WordPress user. This includes the backdoor detection process.
This needs to be followed by a manual backdoor clean-up process where you may need to execute the following steps:
- Detect the problem source and remove the malicious code.
- Install a fresh WordPress version to clean up the infected code.
- Update or delete the installed plugins/themes.
- Clean your .htaccess file or wait for technical help to do the same.
- Check for backdoors by opening your website in incognito mode.
Even if you manage to execute these methods, you would still not be entirely sure if you have managed to remove the backdoor and have prevented future attacks.
Additionally, manual methods are long and time-consuming, thus adding to your frustration.
Are you in a fix on how to get rid of backdoor completely? Don’t be.
WordPress security plugins can help you out! WordPress security plugins are ideal for detecting and removing backdoors as you do not need any technical know-how to use the same.
But first, let’s see what a WordPress security plugin is.
What Are WordPress Security Plugins?
Easy to install, just like any other plugin, a WordPress security plugin can be used to protect your website from a variety of malware attacks, including backdoors.
They are also effective in the removal of backdoor infections entirely from your website.
However, WordPress security plugins also have a few limitations, such as:
- Use of signature matching to detect known malware infections. This form of detection makes it difficult to identify new or relatively unknown malware.
- Malware scanning in WordPress files only and not in database files (a malware attack can also infect that).
All these limitations can increase the turn-around time needed to clean your website from backdoors.
Malcare – Best WordPress Hacking Solution
Hence using a plugin with the above limitation is not recommended as it could lead to Google blacklisting, or your web host is suspending your account.
However, if you are looking for instant malware and backdoor removal along with steps that are easy to implement, the MalCare security plugin is a good recommendation.
I’m using the premium version of this WordPress security plugin and hence recommending the same for you!
Easy to install by any novice WordPress user, MalCare goes beyond simple signature matching to detect malware. This security plugin tool can scan both website and database files for any malware infections.
Additionally, MalCare executes the entire clean-up process on its dedicated servers so that your website servers are not overloaded.
Believe me; it’s as simple as it sounds! It is the best WordPress hacking solution!
Let’s now see how to use the MalCare tool to detect and remove malware from your website.
How To Use MalCare To Remove Backdoors?
Here are the steps you need to execute:
Step 1: Install the activate the MalCare plugin on your website.
Step 2: Once activated it automatically scans your website. Upon finding malware, the plugin notifies you.
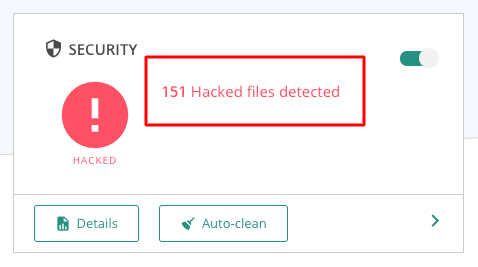
Step 3: Next, in order to clean the site, select the “Auto-clean” button, enter your FTP credentials and the cleaning will begin.
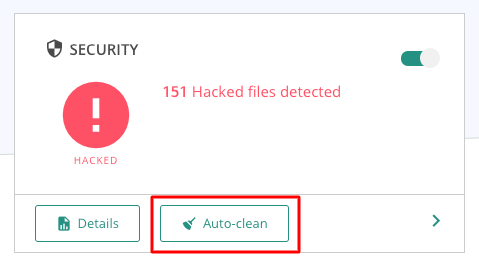
Step 4: That’s all there is to it! MalCare removes the backdoor from your website.
In Conclusion
Implementing security strategies for WordPress is essential! You should not skip this task.
With smart hackers using innovative ways of infecting websites with backdoors, manual methods of detecting backdoors are proving to be insufficient and outdated.
WordPress security plugins are proving to be more effective in detecting malware and backdoor infections, along with completely removing them from infected websites.
This can save you from the constant hassle of having your website hacked over and over again, not to mention the time, effort, and money you can save in the process.
I hope you got the WordPress hacking solution and strongly recommend investing in a trusted security plugin to ensure your site is protected at all times.

I am wordpress User and i always think on Hacker can hack my site but Know i understand what to do…. thanks for Post
very good solutions
Well published. Thanks a lot.
I am also a WordPress user. When hacker hacks my account! I don’t know what was the solution for that. But now clearly know a Hacking solution. Thanks for the post.
I faced this issue a few years ago as someone injected malicious code to steal backlinks from my blog.
Back then, I was using HostGator and I contacted their support team but they couldn’t help me. That’s when I moved to WPX Hosting and they instantly resolved the issue.
That’s also when I realized the importance of using a hack-proof web host like WPX. The best way to stay safe is to use a secure web host and also take regular backups of your blog.
For beginners, stay away from nulled themes or plugins as they mostly contain malicious software. Great points btw!